According to a report from Soluciones Seguras, Costa Rica Organizations are being attacked more frequently in 2021. The main threat is expected to be supply chain attacks aimed at gaining access to legitimate applications that allow them to distribute malware or ransomware on company systems.
“The supply chain has been affected by the inconvenience of containers, however, there is an additional problem we are experiencing, such as cyber-attacks on companies’ internal chains. Attackers have their sights set on vulnerabilities by both the company and the end customer,” says Joey Milgram, General Manager of Soluciones Seguras in Costa Rica.
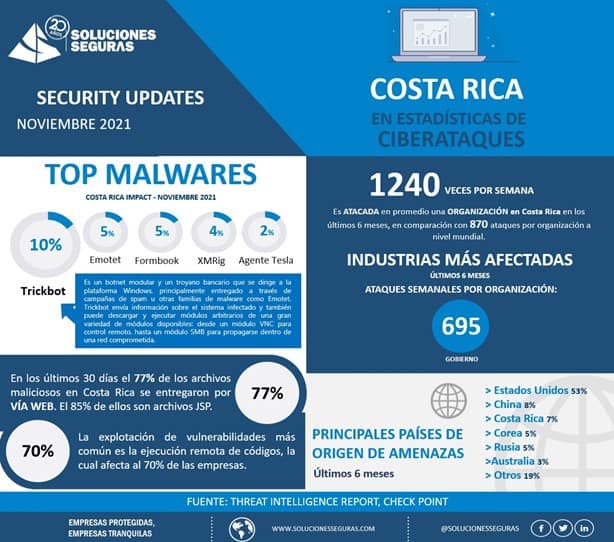
According to the analysis carried out by experts from Check Point, partner of Soluciones Seguras, an organization in Costa Rica is being attacked an average of 1240 times per week and 70% of these were attacked by a “remote execution code”. This code is a cyber attack by which an attacker can remotely execute commands on another person’s device.
Remote code executions (RCE) generally occur due to malicious malware downloaded by the host and can occur regardless of the geographic location of the device.
Cybercriminals are not only looking for opportunities in IT systems, but are aiming to infiltrate what is known as Operational Technology (OT) and Industrial Control Systems (ICS). These are those that handle tasks such as manufacturing, transportation, energy controls, among others.
There are several reasons why cybercriminals are targeting these systems. Among them we can point out
- The increase of automation in processes and supply chain
- The lower level of IT security of OT and ICS, mainly in Latin America.
In addition, this allows them to access some of the most powerful or profit-driven industries in the world, such as oil and gas, automotive, technology manufacturing and pharmaceuticals.
“Although the real impact of these cyber-attacks is unknown, due to the fact that most companies that are affected do not broadcast it to the public. However, weathering these types of attacks has a high cost. Just imagine that an industry, for example, the automotive industry, a manufacturer could see its production stopped for several days,” explains Milgram.
Once they have managed to penetrate the organization, they can choose to infiltrate IT systems or even mission-critical systems, as has happened to several corporations throughout the year, which facilitates the theft or hijacking of information in exchange for a bribe or the obtaining and leaking of information and trade secrets.
Recognizing and analyzing system vulnerabilities is the first step, the expert concludes, to protect operations. A solution that blocks attacks before they reach critical OT systems, as well as minimizing the risk of exposure, should be the priorities.
In the following infographics you will be able to visualize the statistics of cyber-attacks at both the local and regional levels.